Blog / Guide
Write to UsWhat Is an HTTP Proxy?
February 18, 2026
Guide
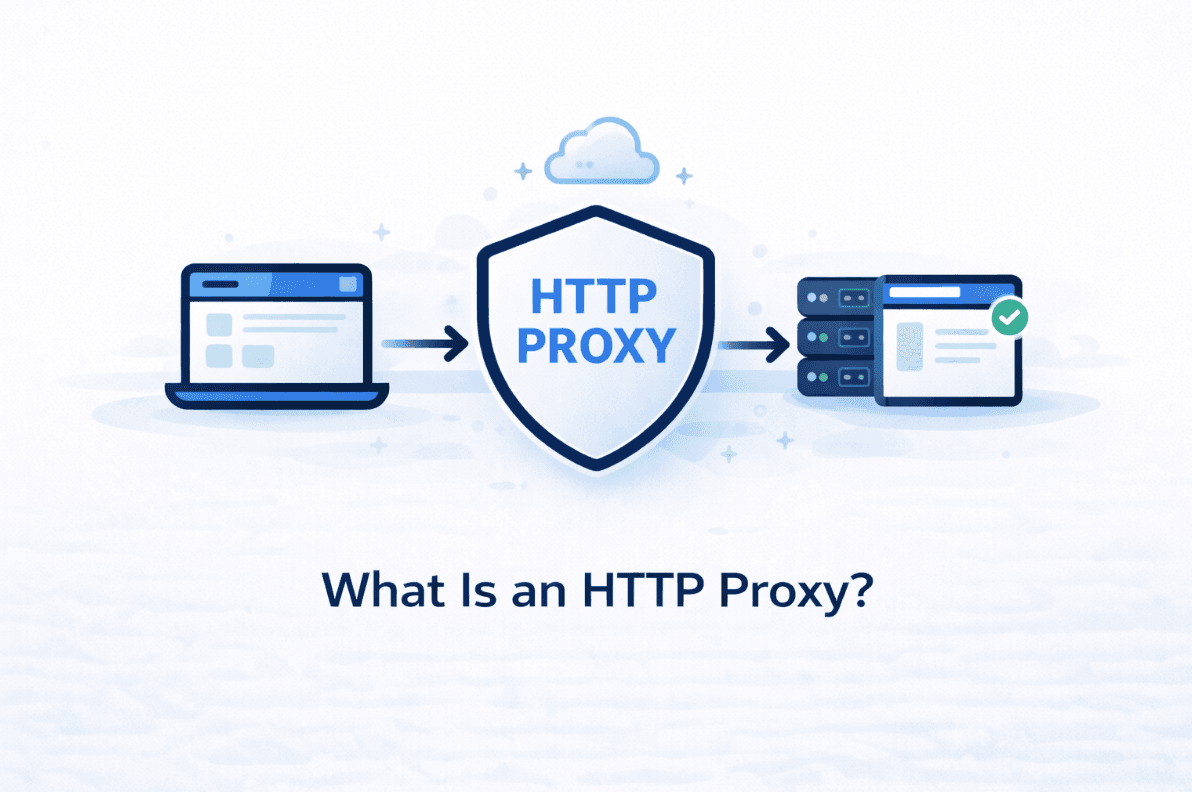
If you've ever changed a setting in your browser, run a scraping script, or worked with automation tools, you've probably seen the option to "use a proxy." Most of the time, that proxy is an HTTP proxy, even if it isn't labeled clearly. An HTTP proxy acts as an intermediary between your device and the web server.
An HTTP proxy is not complicated. It's simply a middle step between you and a website. The hypertext transfer protocol is the foundational protocol for data exchange on the web. Instead of your request going straight to the site, it goes somewhere else first. That "somewhere else" then sends the request onward and passes the response back to you.
What Actually Happens When You Use an HTTP Proxy: How an HTTP Proxy Works
Normally, when you open a website, your device talks directly to the server hosting that site. In this typical setup, the user's computer sends requests straight to the destination server where the website's data resides. Your IP address is visible, the request comes from one place, and everything is straightforward.
With an HTTP proxy in place, the website never talks to you directly. It talks to the proxy. The proxy server acts as an intermediary, forwarding your requests to the destination server on your behalf. As far as the site is concerned, the proxy is the visitor.
Your device never disappears from the process, but it becomes invisible to the destination. The proxy server hides your real IP address by making requests appear to come from the proxy's IP address instead of your own.
Why HTTP Proxies Exist in the First Place
HTTP proxies weren't originally built for anonymity or scraping. They were created to manage web traffic.
Organizations needed a way to:
- Control what users could access
- Cache pages to reduce bandwidth
- Monitor requests
- Analyze network traffic
- Route traffic through a central point
Over time, people realized that the same setup also solved other problems. If requests come from a different IP, then limits can be avoided. If traffic looks distributed, automation becomes easier. If location matters, it can be adjusted.
The use cases evolved, but the core idea stayed simple. HTTP proxies are also used for performance optimization by caching frequently accessed content and reducing network congestion, which improves website load times and overall browsing efficiency.
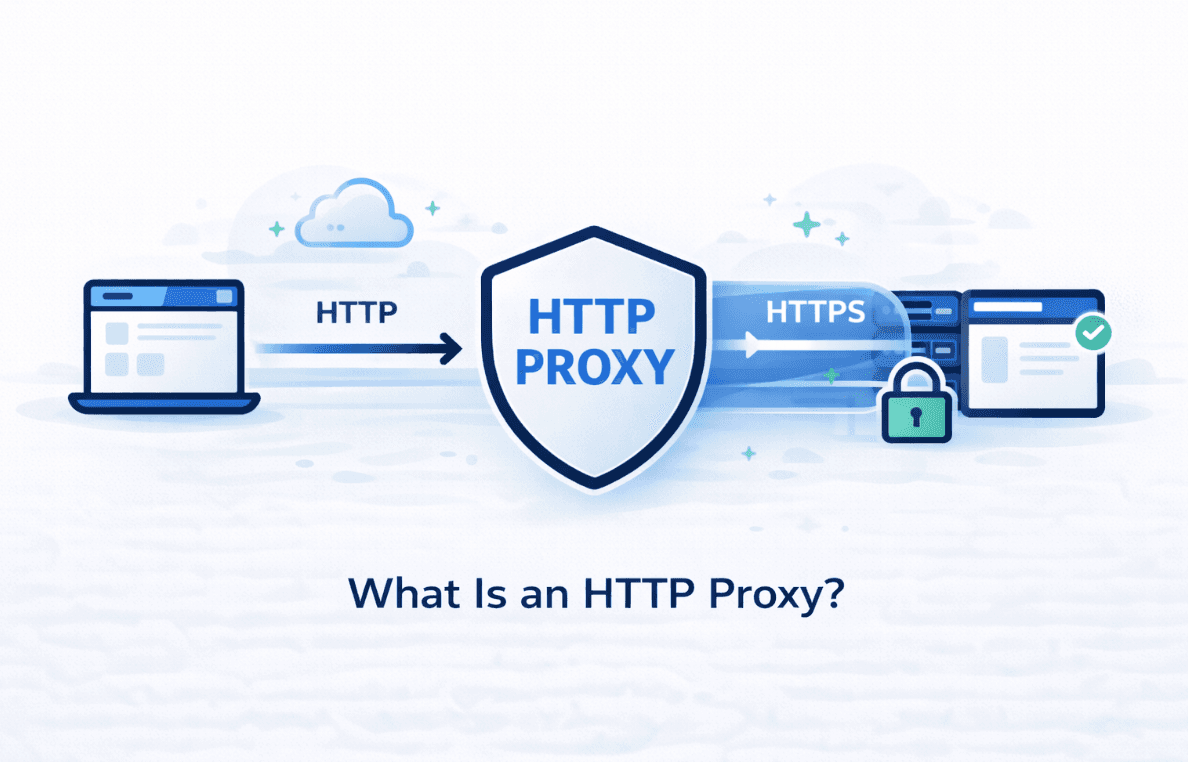
HTTP and HTTPS Are Often Mixed Together
Despite the name, most HTTP proxies today also handle HTTPS traffic. This works through a tunneling method that allows encrypted connections to pass through the proxy without being inspected. HTTPS uses Secure Sockets Layer (SSL) to encrypt data and establish a secure connection between the client and server, ensuring website security and data confidentiality.
The proxy still knows where the request is going. It just doesn't see the content inside the encrypted connection.
That's an important distinction. An HTTP proxy can change where traffic appears to come from, but it does not automatically make traffic private or secure.
Where HTTP Proxies Are Commonly Used
HTTP proxies show up in more places than people realize.
They're used in browsers for basic IP masking. They're used in scripts that send repeated requests. They're used by developers testing websites from different regions. They're used by tools that monitor search results, prices, or availability.
Configuring proxies is straightforward in most browsers and tools, allowing users to easily route their traffic through a proxy.
In many of these cases, the proxy isn't the main feature. It's just part of the plumbing that keeps things running without interruptions. Open proxies are publicly accessible proxy servers that can be used by anyone, but they come with significant security risks.
Content Filtering and Access Control
Content filtering and access control are among the most powerful features of HTTP proxy servers, especially for organizations that need to manage and monitor internet traffic across their networks. By acting as an intermediary between client devices and web servers, an HTTP proxy gives administrators the ability to enforce content filtering policies and restrict access to specific websites or types of web content.
With the right proxy settings, IT teams can block access to certain websites, limit exposure to potentially harmful or inappropriate material, and ensure that sensitive data stays protected. This is particularly important in enterprise environments, where compliance and security are top priorities. By inspecting HTTP requests and responses, the proxy server can identify and filter out content that violates predefined rules, helping to prevent data breaches and reduce the risk of malware or other security threats.

The Limits People Often Miss
HTTP proxies are useful, but they are narrow in scope.
They only affect web traffic. They don't encrypt data by default. Unencrypted proxies can expose login credentials and other sensitive data to interception. They don't protect everything on your device.
And quality matters more than configuration. A badly maintained proxy can cause more problems than it solves. Security vulnerabilities in HTTP proxies can expose sensitive information, potentially leading to data breaches or unauthorized access. Slow connections, unstable sessions, and already-blocked IPs make an HTTP proxy useless very quickly.
This is why people often confuse proxies with VPNs. They solve different problems, even though they sometimes overlap in appearance.
While HTTP proxies can help mask your identity, they do not provide anonymity across the wider internet.
HTTP Proxies vs Other Proxy Types
Compared to other proxy types, HTTP proxies are focused and lightweight. A forward proxy sits between client devices and the internet, managing outbound requests. A reverse proxy acts as an intermediary in front of web servers, handling incoming requests from the internet. A transparent proxy operates at the network level, intercepting traffic without requiring client configuration.
They are easy to set up. They work naturally with browsers and web tools. They do exactly one job well.
Other proxy types can handle more protocols, but that flexibility isn't always needed. If the task lives entirely on the web, an HTTP proxy is often the most practical option. Some HTTP proxies also include a high-performance content filter to efficiently manage and filter web traffic.
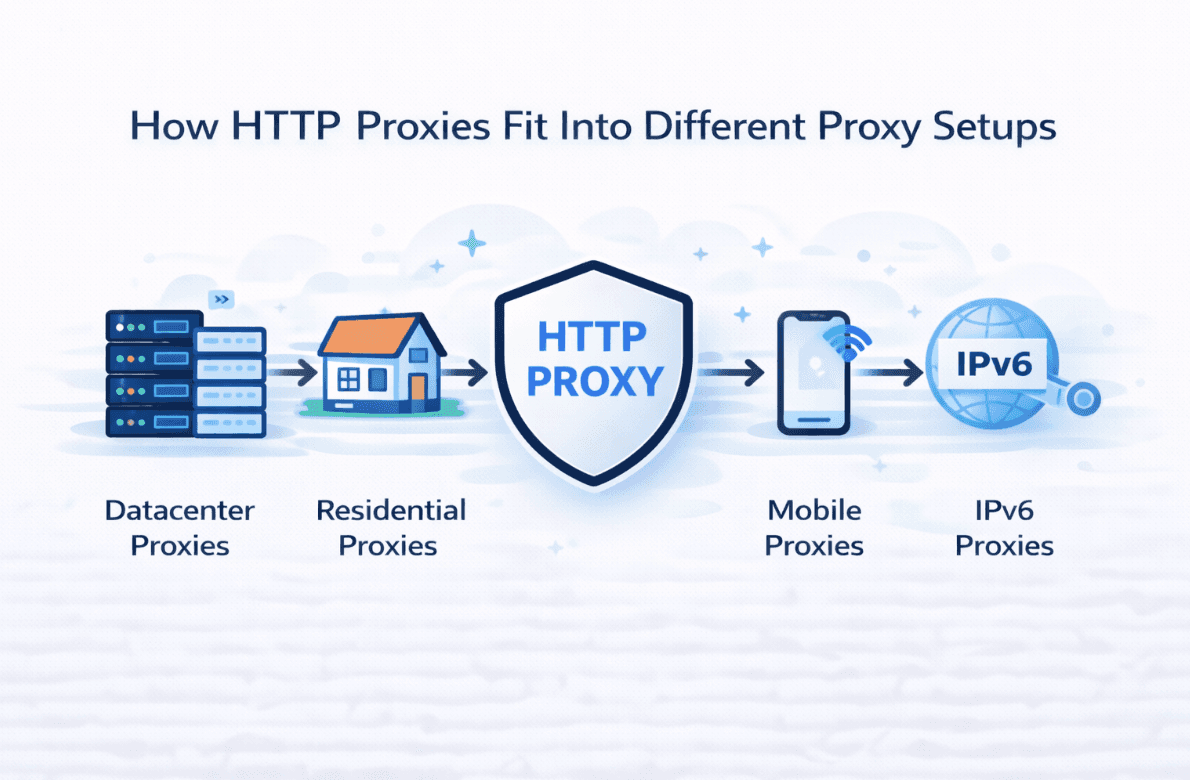
How HTTP Proxies Fit Into Different Proxy Setups
HTTP proxies are not a separate proxy category by themselves. They describe how web traffic is handled, not where the IP addresses come from. In practice, HTTP access is usually available across multiple proxy types, each suited to different tasks.
Some users choose datacenter proxies when speed and request volume are the main priorities. These setups work well for straightforward web automation and monitoring where strict filtering is not an issue.
Others rely on residential proxies, which use IP addresses from real household connections. These tend to blend in more naturally on sites that monitor traffic behavior more closely while still supporting standard HTTP and HTTPS requests.
For platforms with stronger detection systems or mobile-first behavior, mobile proxies are often preferred. Mobile IPs rotate naturally and are commonly shared, which can reduce friction on certain websites.
There are also use cases for IPv6 proxies, which take advantage of the newer IP standard and its large address space, offering an alternative approach for scalable web access.
How HTTP Proxies Are Used Today
Modern applications usually support HTTP proxies without any special setup. You point the application to the proxy, and it handles the rest. An HTTP client sends requests through the proxy, which then forwards them to the HTTP server. In large-scale deployments, HTTP proxies can distribute incoming requests across multiple servers for load balancing and improved performance.
What makes the difference is not the proxy itself, but how it's used. HTTP proxies are often used in enterprise security setups to protect sensitive data and manage access to the public internet. Reasonable request timing, consistent behavior, and realistic patterns matter far more than raw configuration.
Used properly, an HTTP proxy fades into the background and simply allows web interactions to continue without friction. Reverse proxies also manage traffic between the user's device and backend infrastructure, handling incoming requests from the public internet.
FAQ
Is an HTTP proxy the same thing as a VPN?
Does an HTTP proxy hide my IP address?
Can HTTP proxies handle HTTPS websites?
Are HTTP proxies safe to use?
Why do people use HTTP proxies for automation?
Can I use an HTTP proxy in my browser?
What's the difference between HTTP and SOCKS proxies?
December 10, 2025
Guide
What Is a Web Proxy & How It Works
Learn what a web proxy is, how it works, and why LightningProxies is the smart choice for your browsing needs. Discover the differences between web proxies, VPNs, and proxy servers.

October 15, 2025
Guide
Datacenter vs Residential Proxies
Understand datacenter vs residential proxies: how they work, pros/cons, IP rotation, and when to use each for SEO and other tasks.

October 03, 2025
Guide
Proxy Meaning: What Does a Proxy Really Do
Discover the true meaning of proxy servers and how they work.